Business Email Compromise (BEC)
Targets executives or finance teams with the intent to defraud companies.
Business email compromise (BEC) is a type of phishing scam targeting companies for financial gain. These scams typically target executive-level employees or individuals involved in finance that could request or initiate wire transfers or other types of money transfer scams. Cybercriminals sometimes spoof an email address with a similar name of an executive or a vendor familiar with the company. They can also employ spear phishing to access the email credentials of individuals in the organizations and send BEC attacks from compromised accounts. These spoofed or compromised emails are then used to request a fraudulent wire transfer. These BEC attacks lead to millions in losses to companies every year.
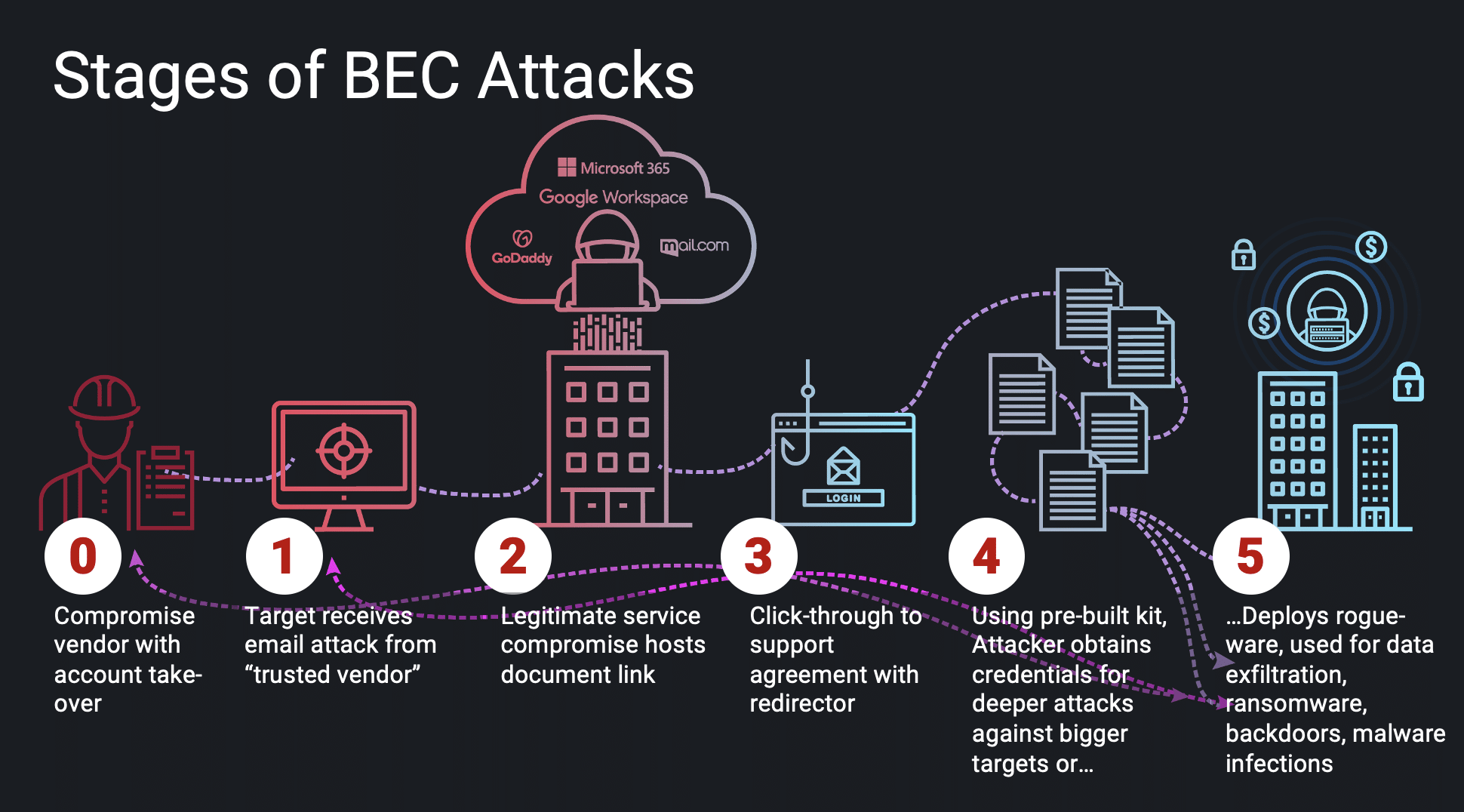
BEC attacks often request for funds to be sent, or wire transferred to pay an invoice or for a service. The targets are often employees that have access to bank information, like accounts payable or finance.
Mostly delivered through email, but cybercriminals are also having success with this type of scam through SMS text messaging. Some sample subject lines include urgent, request for payment, and transfer.
There are five categories of BEC scams
- Fake Invoices- Companies with international vendors are often the target of these attacks, where cybercriminals impersonate vendors requesting fund transfers for payments to an account owned by cybercriminals.
- CEO Fraud: When a cybercriminal poses as the CEO or executive or an organization and asks employees to transfer money or send gift cards.
- Account Take Over When an employee’s account has been hacked and used to request payments using email contacts and sent from the legitimate email address. Then payments are sent to cybercriminal’s bank accounts instead of the actual vendor.
- Attorney Impersonation- Cybercriminals impersonating a lawyer asking for fraudulent requests to gather confidential information.
- Data Exfiltration – HR or Accounts Payable Employees are targeted to obtain personally identifiable information (PII) or tax statements of employees and executives to use in future attacks.
Preventing BEC Attacks Using Generative AI
Cybercriminals are using generative AI – a type of artificial intelligence that can simulate conversations and the written word by doing the thinking faster than a Human – to produce a wide range of outputs, including text, images, music, and more. And this is also where malicious intent through Business Email Compromise (BEC) enters an organization’s door.
Examples of Malicious BEC Activities
Threat actors increase the speed and variation of their attacks by modifying code in malware or creating thousands of variations of social engineering attacks to increase the probability of success. Here are some examples of malicious use:
- An employee is targeted by a scammer who uses generative AI to create an SMS message to impersonate the CEO of the company. The scammer uses the fake message to instruct the employee to transfer funds to a fraudulent account.
- A threat actor uses HR policy announcements and benefits updates to lure victims and steal employees’ credentials.
- Cybercriminal uses generative AI to create convincing fake social media profiles that can be used to impersonate real people or organizations.
- Attackers send text messages to social engineer a victim in an organization into giving valuable financial information or data.
Cyberattacks are most dangerous when delivered with speed and frequency to specific targets in an organization. Tools such as ChatGPT can now create well-written personal emails en-masse with infinite variations, making this method of cyberattacks dangerous to victimized organizations.
SlashNext HumanAI™ Fights Machines With AI Technology
SlashNext fights AI cyberthreats with AI cybersecurity technology to beat malicious threat actors. We’ve been developing natural-language generative AI technology for a year and a half in anticipation of these types of threats.
Generative AI technologies can predict millions of new variants of the threats that might enter an organization, and SlashNext HumanAI is the only way to counteract these AI attacks to close the security gap and vulnerabilities created by this dangerous trend. SlashNext HumanAI adds augmented AI and behavioral contextualization to computer vision and natural language processing (NLP) to detect BEC in email and mobile with unprecedented predictability.
Schedule a Demo or Test Your Security Efficacy in Observability Mode
To see a personalized demo and learn how our product stops BEC, click to schedule a demo or easily test the efficacy of your current email security with no impact to your existing email infrastructure using our 5-min setup Observability Mode.
SlashNext Blog | Business Emai Compromise BEC
Today, while man-in-the-middle (MiTM) attacks are still a big concern, the security endpoint has changed to the browser, creating a MiTB phishing threat that poses real danger.

In recent years phishing has become the number one threat action over malware. Recent workforce changes spurred by the pandemic has led to an exponential increase in phishing attacks.

Just how prevalent are these phishing callbacks and C2 infections? In every client install we perform – 100 percent! – we see C2 infections and callbacks. Are you compromised?
In 2020 phishing exploded as the world faced a 100-year pandemic and many people moved to remote working and learning, which changed the phishing threat landscape forever.
It’s Time to Get Started with SlashNext
Learn how to leverage the industry’s best zero-hour phishing protection and IR solutions in your environment.
6701 Koll Center Parkway, Suite 250
Pleasanton CA 94566
800.930.8643
info@slashnext.com
© All Rights Reserved, SlashNext, Inc.



