SlashNext's AI Platform
The SlashNext platform includes patents for behavioral phishing detection and machine learning to detect unknown threats with unmatched accuracy.

AI-Powered Detection – Breakthrough Results
Greater spear phishing detection vs. top security vendors
Faster average detection time vs. security vendors listed on VirusTotal
Cloud and on-device detection rate with 1 in 1 million false positives
Zero-hour
threats detected daily
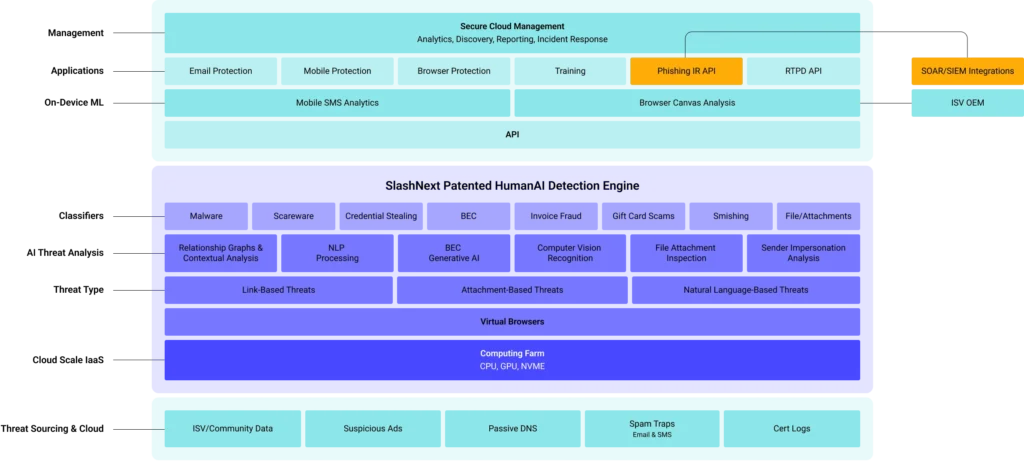
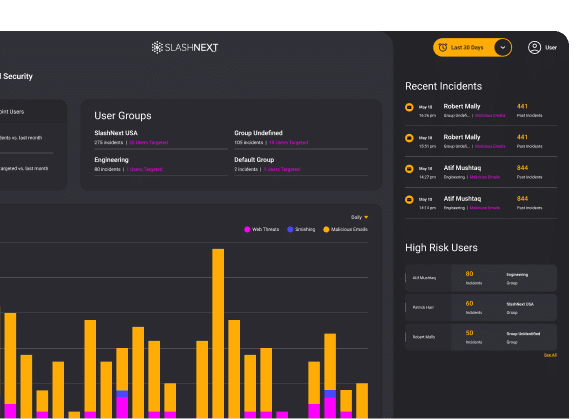
SlashNext Platform Architecture
The SlashNext Advantage is Your Advantage

Preemptive
Global, proactive threat hunting provides advance visibility, detection, and protection from emerging threats
Real-Time
Real-time, automated detection provides more effective protection from zero-hour threats

Extreme Accuracy
Near-zero false positives results in immediately actionable, block-ready threat intelligence
Overcomes Evasion Tactics
Detects threats missed by URL inspection and domain reputation analysis methods

Multi-Vector, Multi-Payload
Covers more types of phishing and social engineering payloads across all phishing attack vectors, not just email
Deployment Flexibility
Deploy to mobile, endpoints, and existing tools and infrastructure
SlashNext's GenAI Threat Detection and Prediction Engine
A unique combination of techniques sees through evasion tactics and accurately detects threats, even those hosted on compromised websites and legitimate infrastructure.
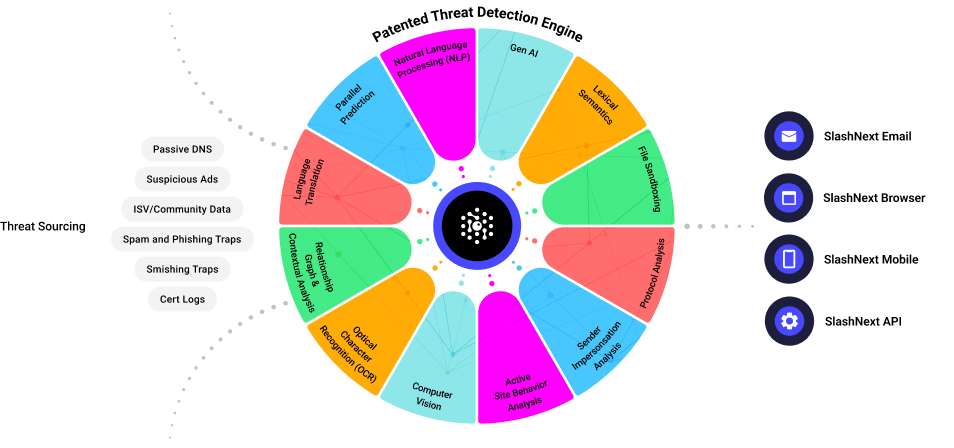
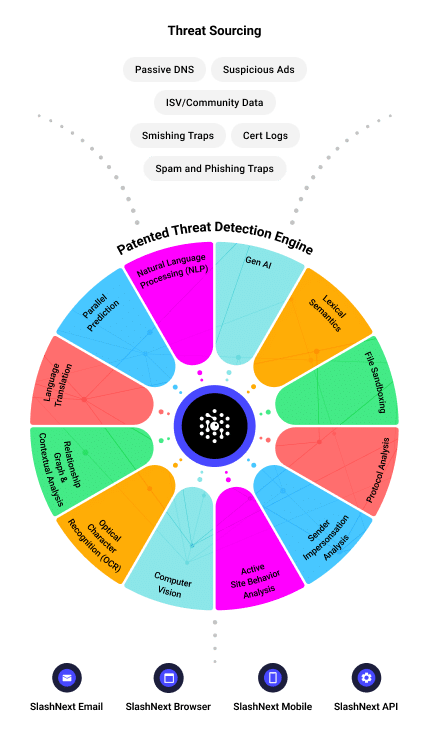
Global, Multi-Vector Threat Sourcing
SlashNext AI technology leverages a global, multi-vector threat intelligence network to proactively source suspicious content. This network includes:
- Global hardware sensors inspecting billions of daily Internet transactions in real-time
- Spam and phishing traps
- Smishing traps
- Suspicious ad networks
- Passive DNS sensors
- Real-time certificate transparency logs
Extreme Accuracy
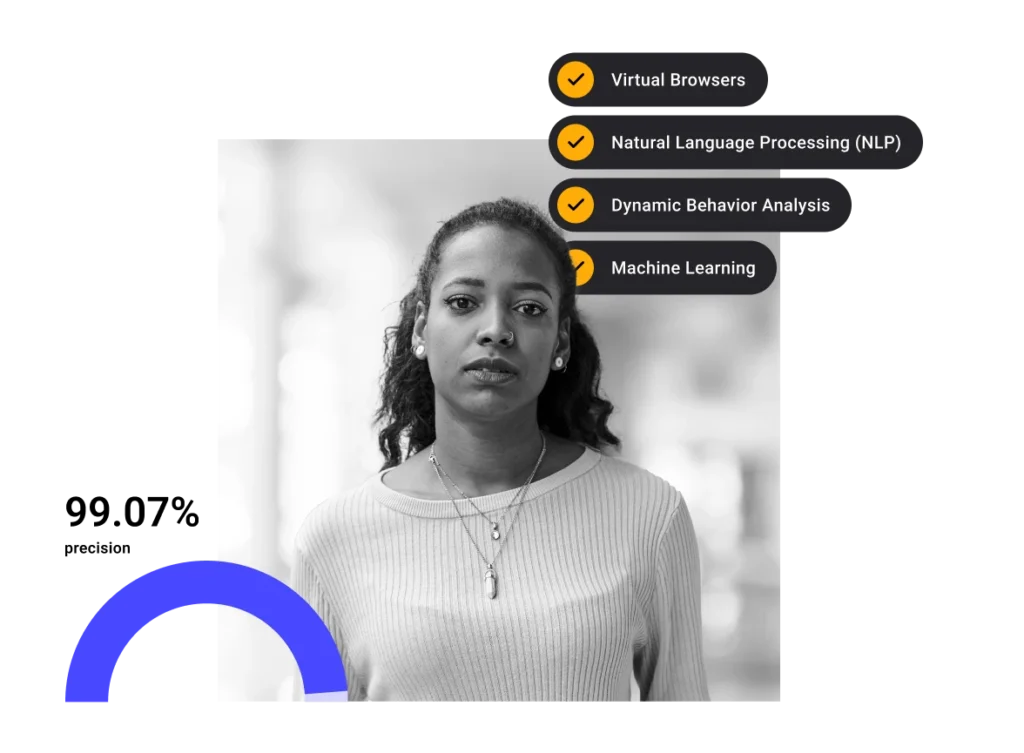
SlashNext’s patented AI technology is purpose-built to anticipate sophisticated threats with a unique combination of next-gen AI technology to stop threats with a 99.9% detection rate and the lowest false positive rate of 1 in 1 million.
- Virtual browsers to dynamically load webpage contents and analyze site behavior
- Natural Language Processing (NLP) and computer vision techniques to understand the textual and visual context of a rendered webpage
- Dynamic site behavioral analysis (fill out forms, analyze behavior, follow re-directs, etc.)
- Mature machine learning algorithms deliver accurate, binary verdicts rather than threat scores
- Relationship Graph & Contextual Analysis baselines your environment and identifies relationship patterns and anomalies
- Generative AI stops advanced BEC to predict tomorrow threats by creating semantical clones to teach the neural network how to detect thousands of variations of attacks
Related Resources
FEATURED WHITE PAPER
The Role of AI in Email Security
New market research, from SlashNext and Osterman Research, reveals email and multi-channel messaging security is a top concern for organizations, as AI plays a pivotal role in the threat landscape.

Featured Blog
State of Phishing Report Reveals More Than 255 Million Attacks in 2022
SlashNext analyzed billions of link-based URLs, attachments, and natural language messages in email, mobile and browser channels over six months in 2022 and found more than 255 million attacks…
FEATURED WHITE PAPER
Microsoft 365 + Integrated Cloud Email Security
Due to the demands of the modern workforce, there has been an exponential shift in the use of native cloud email protection capabilities, like Microsoft 365, in the last 12 months.
See SlashNext Complete™
in Action
Meet with a security expert for a demo and learn how to set up a personalized trial to see the threats entering your organization.


