Thawing Your Email Security Strategy with Frost’s 2024 Radar Report: A Dynamic Cyber Threat Landscape
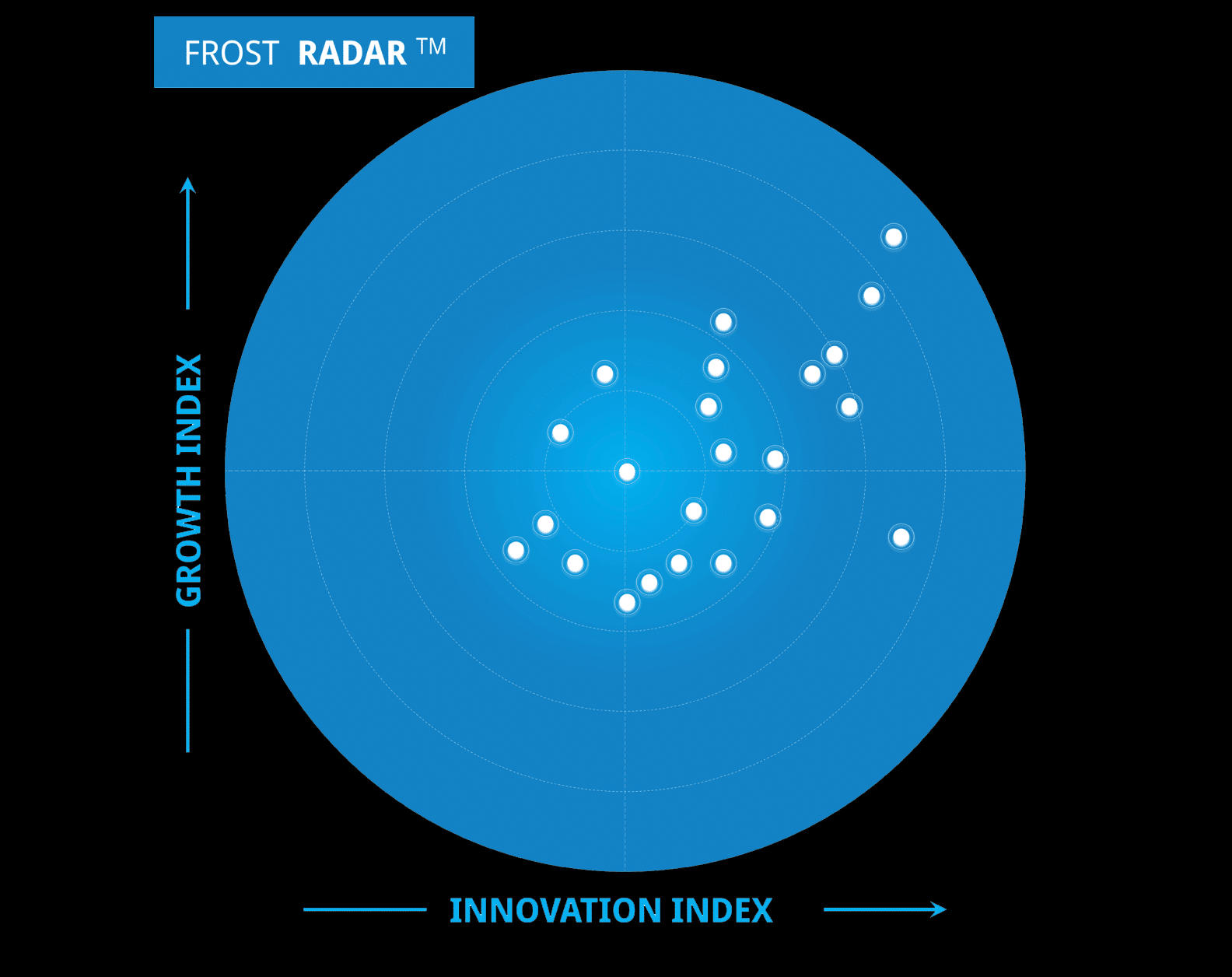
In today's digital age, email remains the primary conduit for business communication, making it a prime target for cybercriminals. The Frost Radar Research Report on Email Security for 2024 underscores…