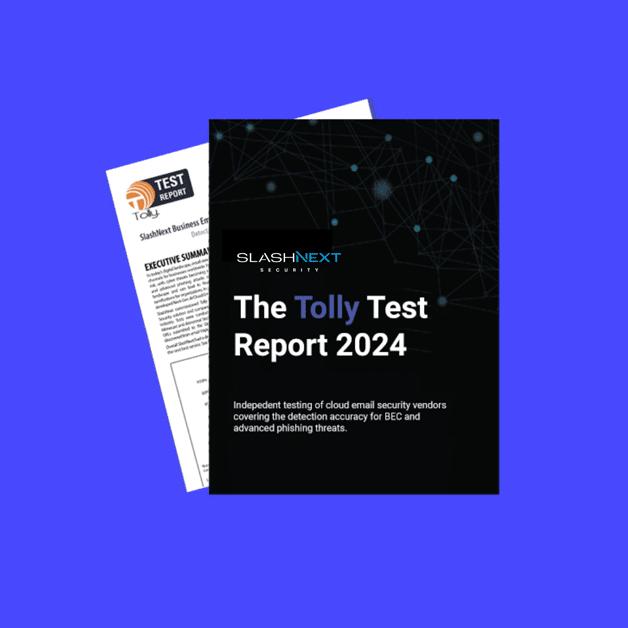
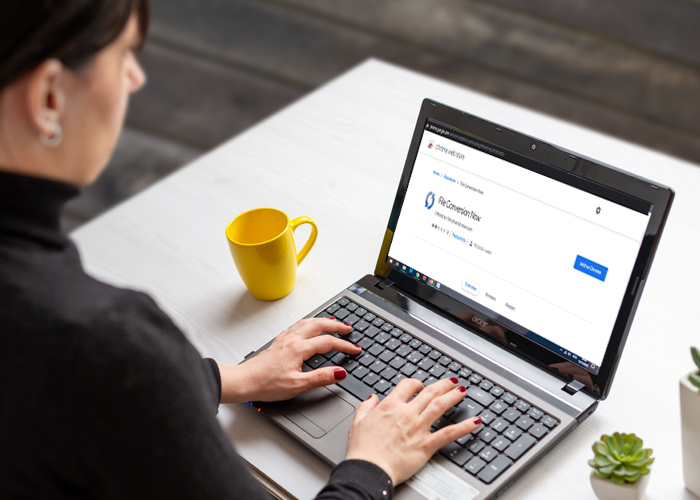
Revamping Email Security: Introducing SlashNext’s Enhanced Administration Portal CMS
In today’s fast-paced digital landscape, ensuring robust email security while maintaining operational efficiency is paramount. At SlashNext, we are dedicated to providing cutting-edge solutions to keep your organization secure from…