Protected with 2FA? Think Again.
Two-factor authentication (2FA) is certainly a best practice for corporate security, but cybercriminals are also quite good at defeating it, often without a user’s knowledge. However 2FA is not a panacea and just like cyber awareness training, it is just one part of a total protection program. Assessing the risk of bypassing 2FA is an important part of any risk assessment, so we thought it would be helpful to review some of the threats we repeatedly encounter that defeat 2FA or multi-factor authentication (MFA).
We often hear when engaging with prospects and customers, “We’re safe. We have 2FA.” And yet, we see malicious schemes that 2FA can be evaded by hackers in multiple ways and fails to protect against phishing threats including scareware, social engineering scams, rogue software, and phishing exploits via weaponized documents. SlashNext Threat Labs routinely sees cyber-attacks that have successfully defeated 2FA and MFA. Here are four examples:
- Man-in-the-Middle Attacks: Many organizations allow employees to use browser extensions that make them more productive, such as specialized ad blockers, file viewers, or file converters. These extensions often have legitimate business functionality, but some also have a side business, and that’s the reason they are free. Their hidden functionality is to act as Man-in-the-Middle spyware in order to collect, use, or sell data, which can include capturing second-factor log-in info, or data that is accessed during that browser session. A browser extension offers cybercriminals the perfect workaround for organizations that rely heavily on 2FA. By design, when a browser extension is installed, it has access to the complete canvas of the browser. This allows it to monitor the session and capture whatever is being rendered on the computer screen. These extensions have the power to see what the user is doing and capture whatever is within that browser window. At SlashNext, we regularly see malicious browser extensions that merely wait for the 2FA to complete. For example, a user logs into a ServiceNow Management Portal, once 2FA is complete, the browser extension starts collecting and secretly transmitted data to a C2 server—exposing important business data to bad actors. With bad actors waiting for the user to log-in legitimately before they start collecting data from the browser, 2FA or MFA ceases to be a viable security option to protect organizations.
- Technical support scams. In addition to rogue browser extensions and Man-in-the-Middle attacks, technical support scams are another way to bypass 2FA security protocols. These phishing scams successfully convince users to install a TeamViewer or some other LogMeIn software, to allow a “tech support expert” to log in remotely to solve their tech problem. However, the TeamViewer session is left open so now a functioning backdoor is open on a device, which is not malware but provides the full backdoor capability to an organization. Access to these compromised machines are then sold on the Dark Web, and even best-of-breed AV will not find them, nor will 2FA have prevented the phishing scheme from accomplishing the goal of compromising the machine.
- Fake 2FA pages or pop-ups. Phishing is so sophisticated today it can easily emulate the authentication websites themselves. Unsuspecting users have presented a login experience that looks just like their normal 2FA experience but is actually a fake site that captures their authentication codes and user credentials. While the actual session token is not compromised, the user is tricked into providing additional security credentials or qualifying data that they might normally provide in a password recovery experience. This data can then be used by bad actors to access one or more corporate systems.
- Scareware. Scareware is another way to obtain the credentials they need to subvert 2FA solutions. Security alerts that look like they come from legitimate providers prompt users to reset passwords due to a security threat or breach. This scareware tactic has been found to target hundreds of Chrome users and the result is successfully bypassing 2FA security protocols.
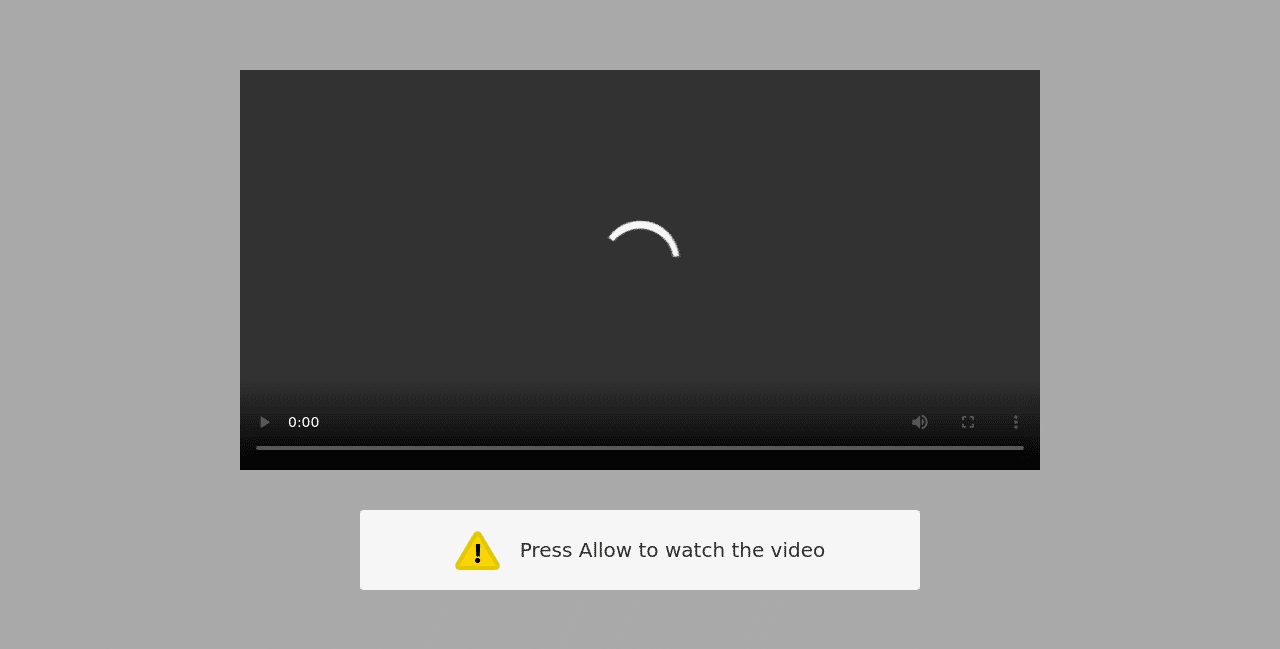
Example 1: Man-in-the-Middle Attack
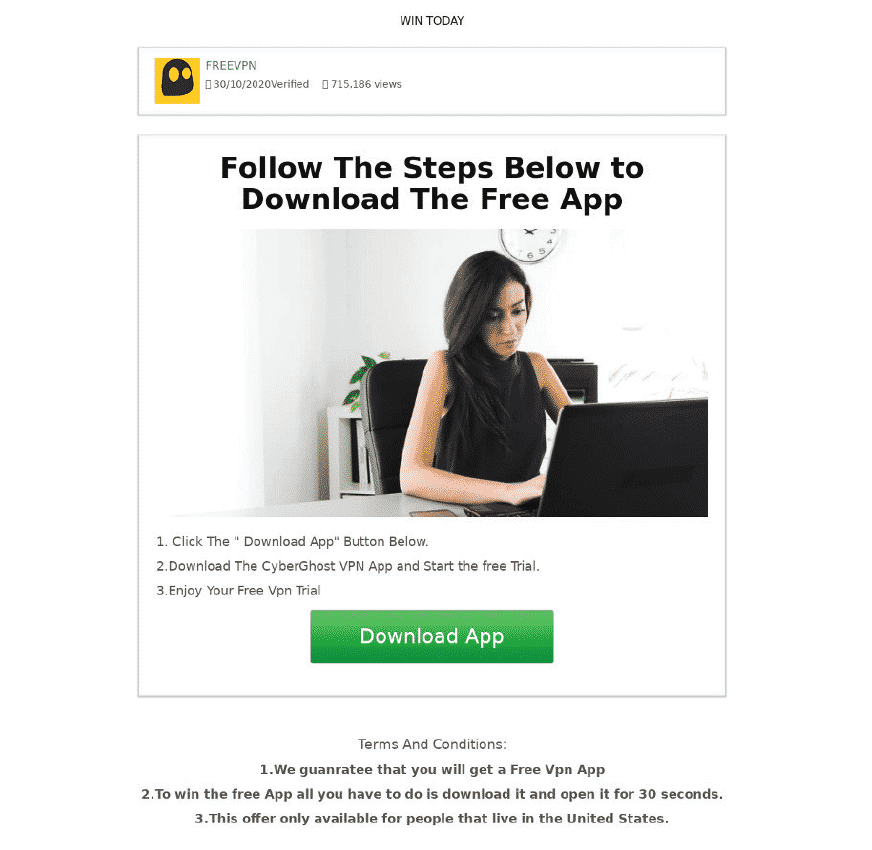
Example 2: Tech Support Scam
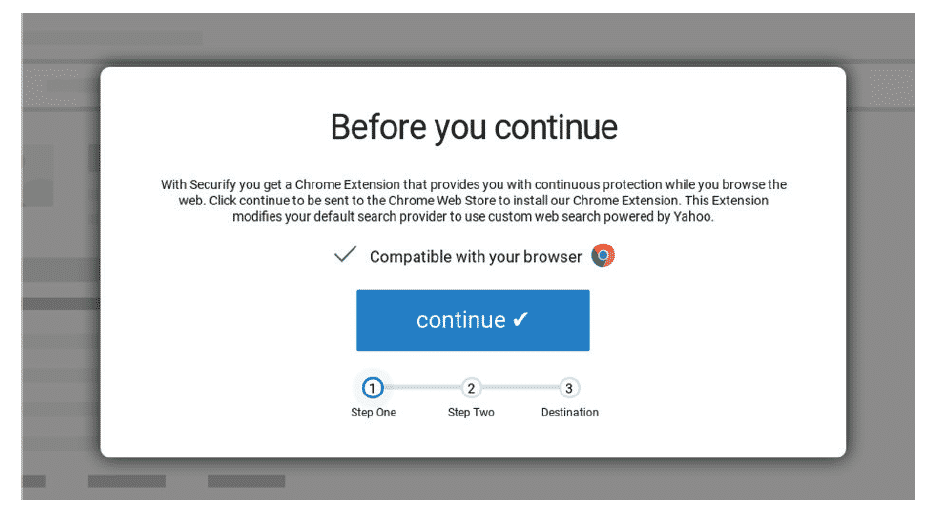
Example 4: Scareware
As 2FA and MFA were designed to help protect unauthorized user log-ins, cybercriminals continue to develop new approaches to access second-factor credentials, spy on browser activity, and compromised machines. SlashNext Total Phishing Protection provides complete protection from credential stealing, rogue software, scams, scareware, and fraud, across email, SMS, social, messaging, and collaboration services.
See what phishing threats you’re missing by taking our Free and Secure Phishing Risk Assessment. Learn more about 2FA threats and more in The State of Phishing 2021 report.


