Why Chose SlashNext Over Abnormal


Abnormal’s relationship graph technology solves half of the problem
Abnormal effectively detects and remediates malicious emails, but its limited multi-channel and multi-payload protections do not address how people work today on mobile and BYOD environments.
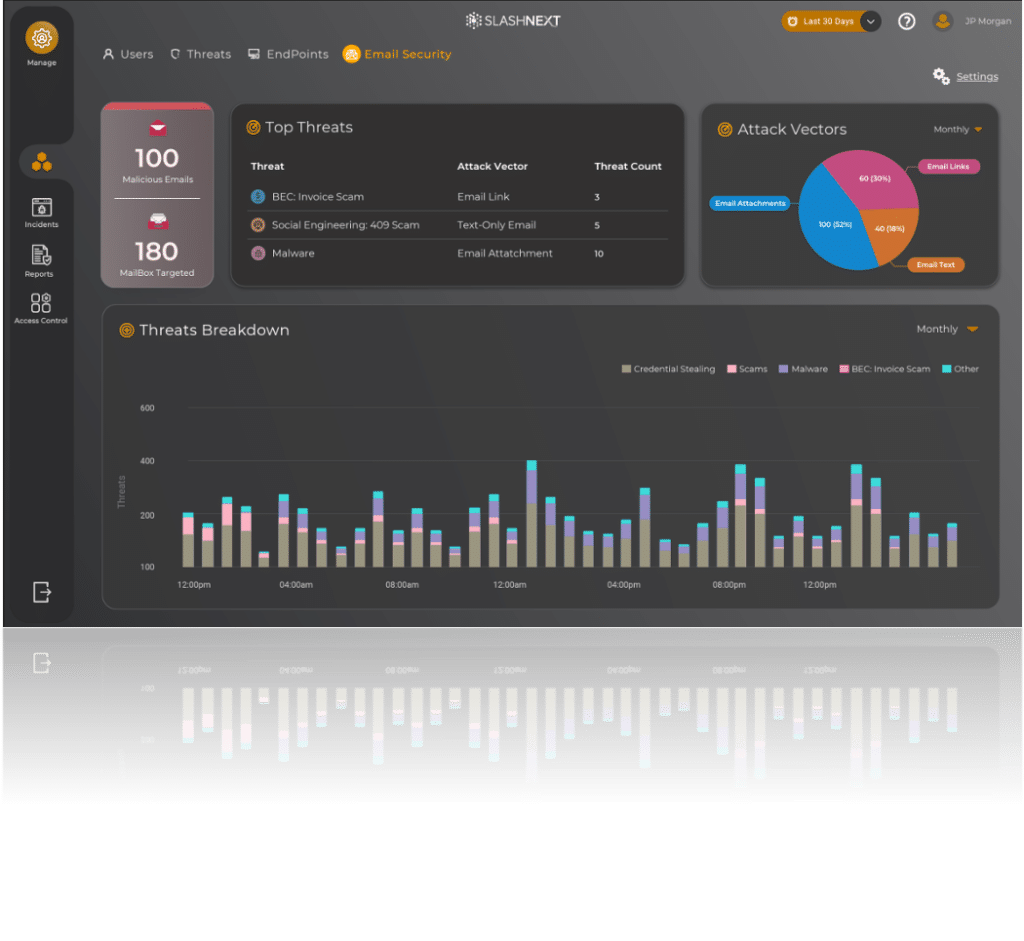
SlashNext is uniquely qualified to achieve complete defense-in-depth security
SlashNext’s Integrated Cloud Email, unique from other ICES solutions, leverages powerful layers of protection with 99.9% accuracy and 1 in 1M false positives.
Multi-phase analysis with relationship graph, contextual analysis, NLP, and computer vision for comprehensive protection
Advanced BEC Protection using Generative AI
- File Attachment Inspection to stop malicious file payloads
- Zero-hour link protection using preemptive sourcing and real-time scans
See How SlashNext Stacks Up Against the Competition
| FEATURE | SLASHNEXT | ABNORMAL |
|---|---|---|
| Zero-hour BEC and ATO Protection Using relationship graph, contextual analysis, natural language processing, and behavioral AI. |  |  |
| Generative AI for BEC and BTC Clones and synthetically generates BEC/BTC threats to train models and continuously predict the next threats. |  |  |
| Relationship Graph and Contextual Analysis Baselines communication patterns to identify relationship patterns and anomalies. |  |  |
| Zero-Hour Link Protection Preemptive sourcing and real-time scans by combining computer vision, NLP, and behavioral AI to identify malicious links. |  |  |
| Zero-Hour File Protection Preemptive sourcing and real-time scans of malicious file payloads, including HTML, doc, pdf, and zip. |  |  |
| Smishing Protection Accurately identify and quarantines malicious SMS/text messages. |  |  |
| Multi-Channel Protection Stops zero-hour threats in apps across M365, Slack, LinkedIn, Zoom, WhatsApp, Telegram, Teams, and other messaging apps. |  |  |
| Operational Security Controls Implement by group, country, and organization, configurable in the admin portal. |  |  |
| FEATURE | SLASHNEXT | ABNORMAL |
|---|---|---|
| Zero-hour BEC and ATO Protection |  |  |
| Generative AI for BEC and BTC |  |  |
| Relationship Graph and Contextual Analysis |  |  |
| Zero-Hour Link Protection |  |  |
| Zero-Hour File Protection |  |  |
| Smishing Protection |  |  |
| Multi-Channel Protection |  |  |
| Operational Security Controls |  |  |
Trusted By Our Customers
8 Million Mailboxes, Devices and APIs Protected
Catches what Microsoft missed.
Solutions Development EngineerMid-Enterprise 
SlashNext is state of the art technology.
Chief Information Security OfficerLarge Enterprise 
Phishing defense easily deployed for thousands of employees.
Vice President, Security ArchitectLarge Enterprise 
Excellent product. Helped narrow the email attacks against our mobile fleet.
Security Operations Large Enterprise 
Superb product. Works great and is easy to setup.
CISOMid-Enterprise 
Compare SlashNext with your current email security solution
- Set up in minutes without impacting your existing email infrastructure or mail flow
- Full visibility and immediate transparency of threats identified in your environment
- Get personalized insights into how we do it